Zero-Knowledge Cryptography: Maintaining Secrecy with Zero-Knowledge Proof
Trying to stay in the loop regarding cryptography concepts? You’re in the right place! Today, we’re discussing zero-knowledge proof (ZKP) in cryptography. We’ll explore why cryptography needs ZKP, explain zero-knowledge cryptography in simple terms, and see how it facilitates cryptographic standards of anonymity and privacy. Take it away!
Basics of Cryptography
The usage of cryptography as a science can be traced back to at least 2000 BC. Its first applications included encryption of military communications in Ancient Egypt - even if the messenger was to be captured, the enemy wouldn’t be able to read the encrypted message. And so, until recently, cryptography traditionally referred primarily to encryption, i.e. converting plain text into an unintelligible form that only another person with the correct key could decipher.
This changed radically with the appearance of the first computers in the mid-20th century. Huge developments in practical cryptography were made, and so the term "cryptography" grew far beyond simply "secret writing".
Nowadays, cryptography is centered around protecting information interactions based on the transformation of data. It uses secret algorithms, which can in turn use secret parameters. Such information interaction occurs between two or more subjects, with the main content being the transmission, and sometimes processing of information.
Why Cryptography Needs Zero-Knowledge Proof
By now, plenty of cryptography tools and approaches have been invented to ensure the protection of information interactions. However, they only work if both the sender and the recipient have the key, e.g. know the correct password. But what if you wanted to confirm that you do, in fact, have the correct key, without sharing it with the other party? That’s when you’d need zero-knowledge cryptography.
Examples of situations where you may require zero-knowledge proof cryptography:
- You have to prove your age without revealing it.
- You want to pay with your credit card on a third-party website, but don’t want to share your banking details with it.
- You need to prove to a third party that you know the correct password without telling them the password.

Stay on top of security with Passwarden - one of best password managers
Note: Passwarden is also available as a part of the MonoDefense® security bundle.
Basics of Zero-Knowledge Proof in Cryptography
Technically speaking, Zero-Knowledge Proof (ZKP) is a cryptographic approach where no information is shared during an interaction except for some value known to both ends of the process (the prover and the verifier). In layman’s terms, zero-knowledge proof means that you can prove to someone that you possess a piece of information without actually revealing the information itself.
Common ELI5 example of zero-knowledge proof cryptography:
The Ali Baba cave
Peggy (the prover) has uncovered the secret word to Ali Baba cave. She wants to prove this fact to Victor (the verifier) without revealing the word itself.
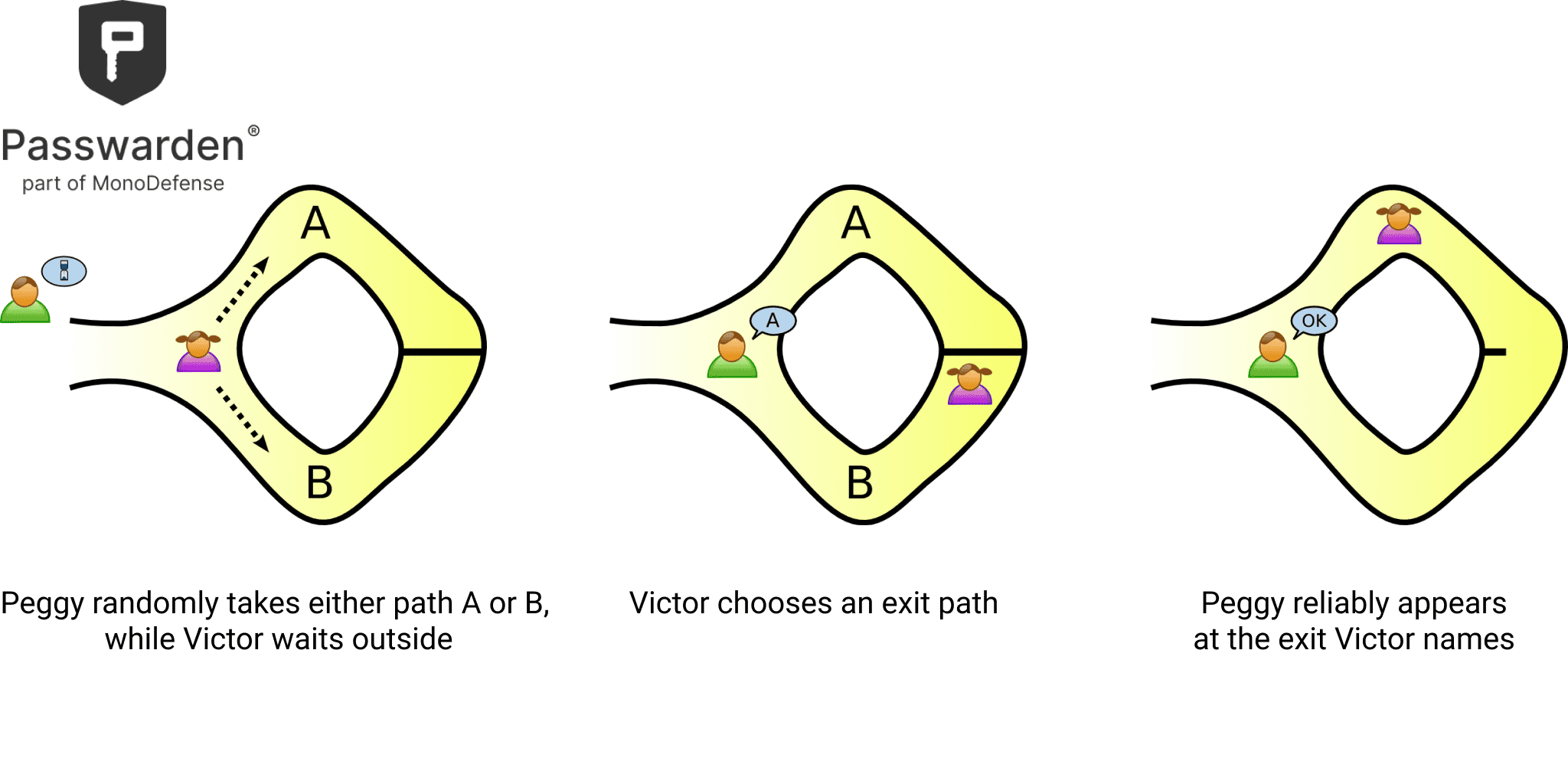
The cave in this example is a bit weird but stick with us. It is shaped like a ring, there’s the entrance on one side and the magic door blocks the way on the opposite side. The left and right paths from the entrance are labeled A and B, respectively.
Victor waits outside the cave as Peggy goes in. Then, she takes either path A or B, but Victor can’t see which. Next, Victor enters the cave and randomly shouts the name of the path Peggy should use to return, either A or B. Providing she really does know the magic word, Peggy opens the door (if necessary) and returns along the desired path.
Now, Peggy could have guessed which path Victor would choose. However, if they repeat this trick many times in a row, she won’t be able to successfully anticipate all of Victor's requests. So if she manages to return via the path Victor chooses every time, this proves that she indeed knows the secret word, without revealing the password to Victor.

Stay protected even without ZKPs
Traits and Benefits of Zero-Knowledge Cryptography
To be considered zero-knowledge proof, a cryptographic interaction must meet three requirements:
- Completeness - the verifier has to permit the prover to process the transaction ahead once the transaction is verified.
- Soundness - the transaction is permitted only if the prover is correct; the verifier cannot be convinced otherwise.
- Zero-knowledge - the verifier cannot have any information and private data, other than the current statement and that it’s true or false.
Advantages of zero-knowledge cryptography
- Simplicity is a notable attribute of ZKPs. Zero-knowledge cryptography requires comparatively less software knowledge to operate while offering superior and impactful solutions. It also offers an interesting security alternative to common encryption.
- ZKP cryptography is extremely secure when it comes to interactions and information exchange.
- ZKPs can be a time-saver, shortening the time required in blockchain transactions.
- Zero-knowledge cryptography protects the users’ privacy by never requiring them to share sensitive data.
- Safety is another huge benefit. Users of zero-knowledge proof cryptography can stay away from any company or website that asks for their personal information and sensitive data without a valid reason.
Applications of Zero-Knowledge Proof Cryptography
Login/password authentication
Probably the most obvious one, ZKPs allow you to exchange your login and password in an open (unencrypted) form. You won’t need any encryption, since zero-knowledge cryptography then proves that both you and the server know the correct password.
Request by ID
ZKPs can be used to authenticate requests to sensitive data. For example, if your bank is asking the Credit Rating authority for your credit rating score via your SSN, it is directly revealing the fact that you are the bank’s client. However, if the bank only uses your name, which is a very broad identifier, the interaction only succeeds if the authority has some record(s) matching the desired SSN.
Voting
Electronic voting, to be precise. It already has plenty of advantages, and zero-knowledge cryptography can add another one - totally transparent vote counting with every citizen being able to verify that the votes are counted correctly.
Protect your passwords and data with Passwarden!
Get the most up-to-date protection and information!